Articles March 8, 2024
Accessibility Considerations for Authentication Experiences


What Is Required for Legal Compliance?
General Accessibility Considerations

Neurodivergent Users
The term "neurodivergent” encompasses people with differences in learning, mood, attention, social skills, literacy, and numeracy. Conditions such as Attention Deficit Hyperactivity Disorder (ADHD), Dyslexia, Dyscalculia, Tourette's Syndrome, Dyspraxia, Autism, and Asperger's Syndrome are among the examples of neurodivergent conditions. It’s estimated that at least 15% of the population is neurodivergent (Reciteme, 2023).

Access to a Mobile Device
Many methods of authentication, particularly in multifactor authentication, require the user to own and have immediate access to a mobile device. For a variety of reasons, disabled users may be less likely to own a phone or be able to access it quickly when required.

Holistic Accessibility Matters
Simply put, the accessibility of any authentication experience is dependent on all of the tools, content, and functionality involved meeting accessibility standards and supporting use of assistive technology. Ultimately, it doesn’t matter what method you choose to authenticate your users if your login screen or authenticator app still present accessibility barriers.
Common Authentication Methods

The most traditional and common authentication method is entering a custom password previously selected by the user.
- Passwords can be difficult to remember, particularly for users with learning or cognitive disabilities.
- Additionally, as password requirements become more involved and passwords grow longer and more complex, accurately entering a password can prove challenging for many users, such as those with limited mobility, reduced fine motor control, or reading disabilities like dyslexia.
- That said, it should be noted that there are tools commonly available to help users here, such as password managers that can store and auto-populate a password.

Temporary passwords or PINs present many of the same memory and transcription challenges as custom passwords but lack access to supporting mechanisms like password managers.
- In many cases, users must also jump between devices in order to locate and then enter the temporary password or PIN, requiring context switching that can present challenges for many neurodivergent users.
- Finally, these patterns typically have time limits associated, which can further increase the difficulty and likelihood of error.
A one-time-use email link (or “magic link”) can serve much the same purpose as a temporary password or PIN – to confirm a user’s ownership of an email account or phone number during account setup – or as the primary method to log in.
- However, compared to temporary passwords or PINS, magic links have a much lower interaction cost for the user, and therefore fewer potential accessibility issues.
- These links usually have a short time limit before they expire, which can still present challenges for users if they are not long enough.
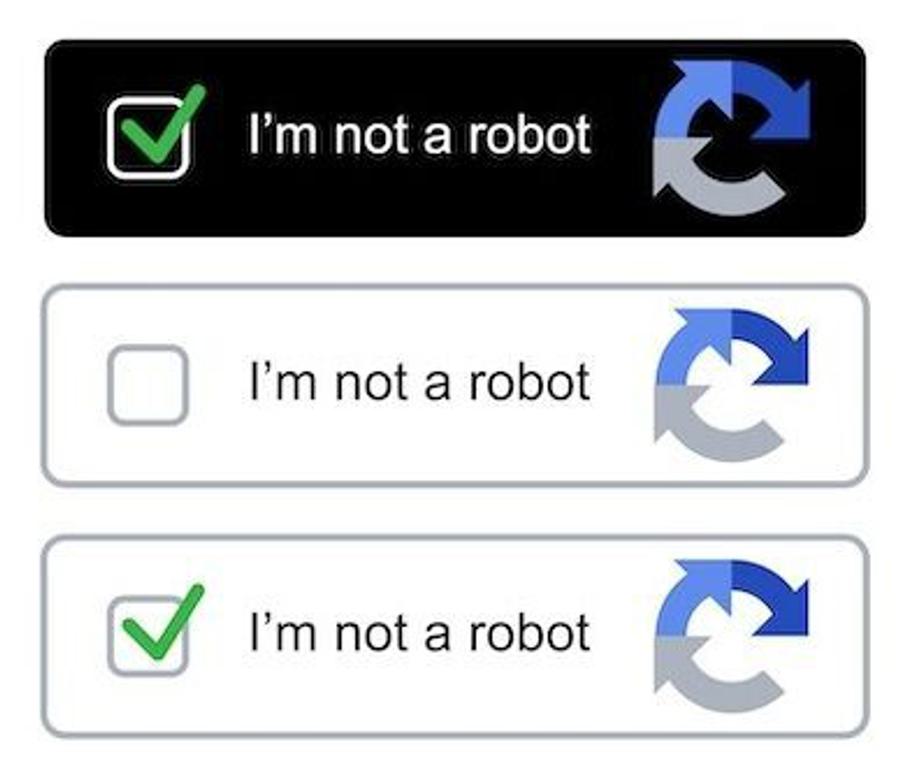
CAPTCHAs are often used in authentication flows to validate that the user is human and prevent bot attacks.
- They require the user to complete a brief test, such as transcribing the letters shown in an image or selecting a particular type of object.
- Many CAPTCHA solutions also provide an audio alternative for blind or low vision users, which asks the users to transcribe numbers or words from an audio recording.
- Unfortunately, neither variety is accessible to deafblind users. CAPTCHAs can also present barriers for neurodivergent users who may interpret the challenge differently than intended, or may struggle to complete it correctly.

QR codes can be seen in multifactor authentication schemes, usually through an app on the user’s device.
- These are a very appealing option for many users since they do not require the user to transcribe a password or pass a test.
- Nevertheless, QR codes can be difficult to locate and scan for blind or low vision users, though some screen readers have useful features to assist with this.
- Users with tremors, reduced fine motor control, and other physical disabilities may also struggle to successfully scan a QR code.

Biometrics, such as facial or fingerprint recognition, generally present a low cognitive load and interaction requirements, which makes them helpful to many disabled users.
- However, biometrics may still not be a silver bullet for all users.
- For example, those with mobility impairments may struggle to maneuver their body and/or device to successfully scan their face or fingerprint, and users with visual disabilities may find it difficult to set up and use mechanisms like Face ID.

Physical security tokens, such as a USB dongle that the user plugs into their computer, also typically require minimal additional input from the user and can alleviate many of the accessibility concerns involved with more traditional authentication methods like passwords. However, they can be easily lost or misplaced, which may be a greater concern for many neurodivergent users.